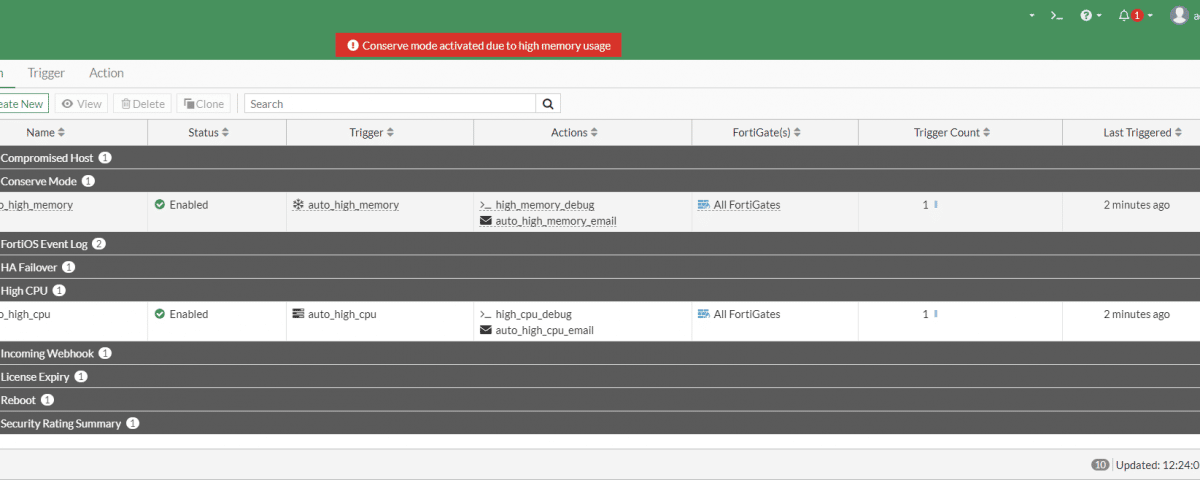
Description
By default, FortiOS will spawn as many IPS , WAD, AV and SSL-VPN processes as CPU cores available on a device. Since each process is consuming memory, and a memory size on an entry level firewall ( Fortigate 30-90e models , also F models ) is very limited, these processes can consume enough available memory to force Fortigate firewall in conserve mode due to a high memory usage.
We have observed this happening on firewalls running 6.4, 7.0 and 7.2 firmware.
Workaround
The only workaround we were able to find is to limit amount of processes spawned by IPS , WAD and SSL-VPN engines
In a CLI prompt, run following commands
config system global
set miglogd-children 1
set sslvpn-max-worker-count 2
set wad-worker-count 2
set scanunit-count 2
end
config ips global
set engine-count 2
endThis will force FortiOS to lower number of processes for scan engines and you should see firewall going to a normal mode is a few minutes.
Please note that in HA cluster, you will need to run these commands on both primary and secondary device, since these settings are not replicated between cluster members.
This article is based on information from this Fortinet’s Knoweledge article .